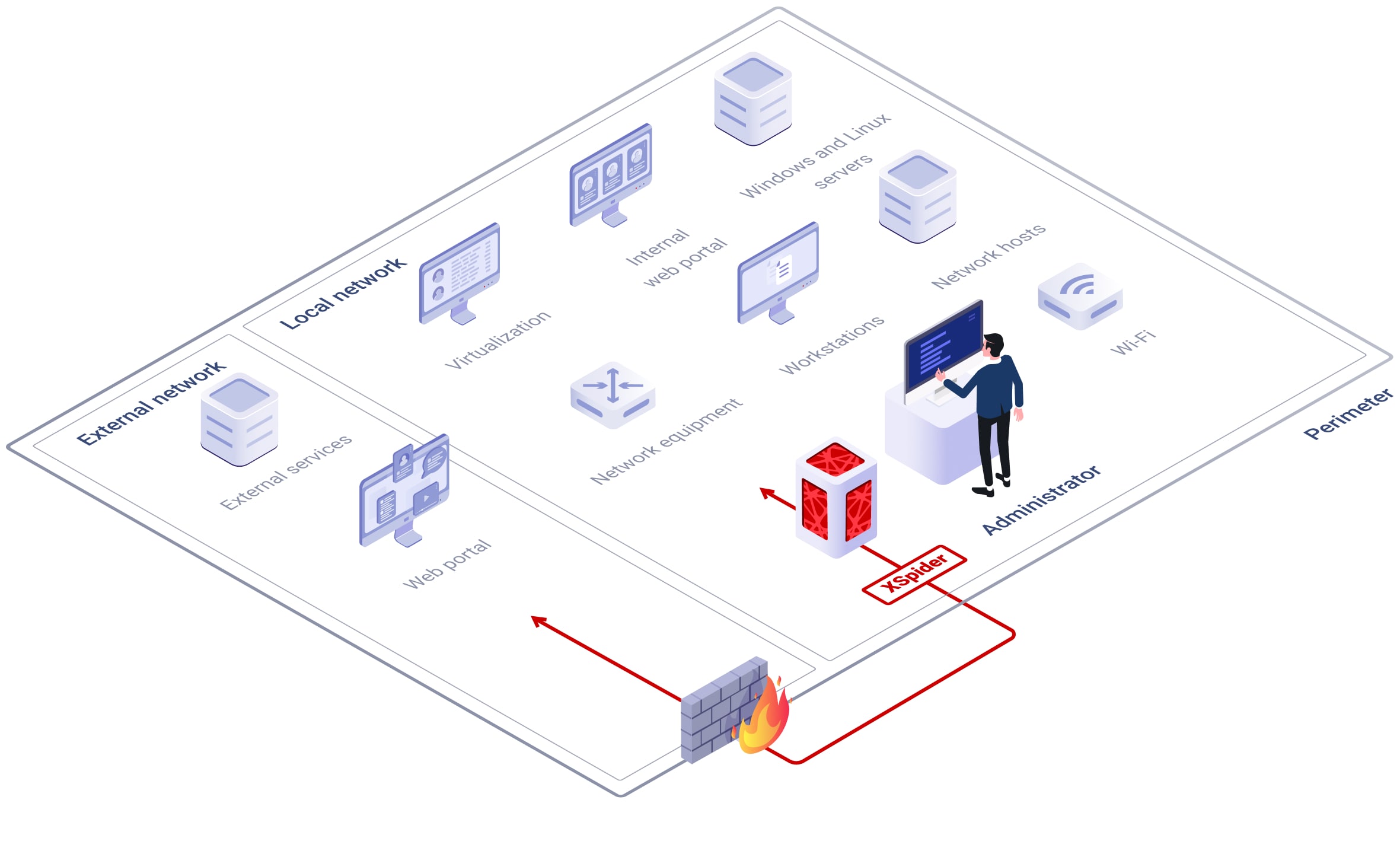
XSpider is a vulnerability scanner for seeing the real state of security on your IT infrastructure. Quickly and precisely enumerate your network components, scan network resources for vulnerabilities, and get recommendations for remediation.
XSpider is a vulnerability scanner for seeing the real state of security on your IT infrastructure. Quickly and precisely enumerate your network components, scan network resources for vulnerabilities, and get recommendations for remediation.